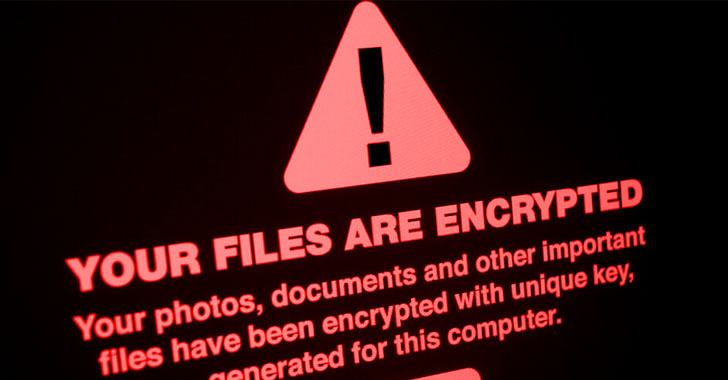
The recent influx of ransomware attacks has brought to life fears of downtime and data loss cybersecurity pros have warned about, as attacks on the energy sector, food supply chain, healthcare industry, and other critical infrastructure have grabbed headlines. The only war to combat the rise in ransomware is to strengthen the defenses to stop it from affecting millions.
In this respect, Ransomware is one of the most dynamic and stealthy threats on the market today. It’s fast-moving and represents a major cybersecurity concern for organizations of all sizes.
There are multiple developments that are encouraging in this regard, however. For example, a recent report by global consultancy firm Kroll indicated that only 2% of ransomware attacks have been reported to police authorities in spite of a 60% increase in monetary losses from 2015 to 2016.
While many security professionals believe that there is a general lack of awareness and education in this space, some have observed that attackers are increasingly choosing to focus on high-value targets where they know their malware will garner the most attention. Fixing these issue could help strengthen your business’s ransomware defenses.
1. New Strains Overwhelm Old Defenses
The first way to strengthen your ransomware defenses is to know how the malware works and how if your current defenses might be out-of-date. Many new ransomware strains now act like advanced persistent threats (APTs), lying dormant in the corporate networks for weeks, quietly gathering information and stealing data.
The most recent example of this is the “Swift” attack that occurred in 2017 when attackers leveraged a vulnerability in Microsoft Excel to infect victims with malware. This attack was later found to be an early effort by the Lazarus group, one of the most sophisticated cyber-criminal groups ever encountered.
While those infected were able to get their hands on $1.6 million worth of compromised data, there were few repercussions. Their attacks had been chronicled in previous years but authorities were never able to pinpoint who was responsible for them.
Organizations cannot continue to rely solely on signature-based defenses to stop cybersecurity. Instead, they must learn to strengthen their defenses to stop the “low and slow” attacks used by many sophisticated hackers.
Organizations must implement more adaptive defenses that use behavioral-based detection to identify and stop threats. Solutions powered by machine intelligence – the next stage of artificial intelligence and machine learning – are adept at recognizing new patterns of attack behavior and automatically respond in real-time to mitigate the attack.
2. Better Processes Stop Ransomware
While using modern solutions to defeat modern threats is critical, upgraded defenses alone are not enough in a world where ransomware is considered an inevitability by experts.
Instead, organizations should focus on upgrading their incident response processes by working with incident response teams to develop a way to gather useful information from different sources and use this intelligence as evidence that can be used in investigating crimes under the Computer Fraud and Abuse Act.
When an organization is able to identify patterns, it’s easier to then investigate the source of these attacks and prosecute criminals who are responsible for them. This helps keep the cybercriminal community accountable for their actions, making them think twice before they strike again.
3. People Aware of Ransomware Avoid It
Combatting ransomware falls down, though, if people aren’t involved in protecting the company. Security awareness training is as vital to endpoint security as is defensive technology. Just training end-users to recognize and avoid social engineering attempts could go a long way to strengthen and preventing an attack from succeeding.
Security awareness training comes in a variety of forms. For instance, it might involve showing employees how to use two-factor authentication to prevent phishing, or what to do after they have been infected. A great resource for this is the Center for Internet Security’s WHISKY cybersecurity awareness training document.
4. Hackers Distrust Payment Channels
Ransomware creators believe that including “ransom” into their encrypted files and demanding payment for decryption keys will deter people from paying in the first place. However, many ransomware creators are now realizing that they will get better results from keeping the keys to decrypt their files with no payment involved.
Instead of paying the attackers directly when they encrypt a file, victims should make a payment to the credit card associated with the email address used to get infected. Doing this would help them circumvent ransomware for good.
For this reason, more and more ransomware creators are going directly after wallet-stealing malware in attacks instead of requesting money from their victims.
![]()
If you would like liquidvideotechnologies.com to discuss developing your Home Security System, Networking, Access Control, Fire, IT consultant, or PCI Compliance, please do not hesitate to call us at 864-859-9848 or you can email us at deveren@liquidvideotechnologies.com.

Recent Comments