440 Million Android Users Plagued By Extremely Obnoxious Pop-Ups
The mobile ad plugin, found in hundreds of Google Play apps, uses well-honed techniques from malware development to hide itself.
Over 440 million Android phones have been exposed to an obnoxious advertising plugin hidden within hundreds of popular applications available via Google Play, which ultimately can render phones almost unusable.
Lookout Research discovered the plugin being bundled with 238 unique applications that have racked up millions of downloads between them – all from one company in China, CooTek. Dubbed BeiTaPlugin, the ad module forcibly displays ads on the user’s lock screen, triggers video and audio advertisements (even while the phone is asleep) and displays out-of-app ads in other areas too.
“Users have reported being unable to answer calls or interact with other apps, due to the persistent and pervasive nature of the ads displayed,” Lookout said in a posting on Tuesday.
Developers of free mobile apps turn to advertising plugins to monetize their wares. These automatically fetch ads at specified times to display, usually within the context of the application itself. For instance, when a player completes a level in a mobile game, he usually has to suffer through a 30-second ad before being able to go onto the next challenge.
However, out-of-app ads skirt the line between legitimate business modeling and obtrusive scamminess by pushing pop-up ads to users when they’re doing other things. The offending app could push an ad to the notification area of the phone, or present a pop-up anywhere, anytime – and the unfortunate part is that the user wouldn’t know which app is the one being obnoxious.
Users in the on an Android forum discussion were monitoring their devices and came to this conclusion:

BeiTaPlugin takes this dodgy practice to an entirely new level, according to Lookout, by employing obfuscation techniques normally reserved for standard malware in order to hide from utilities that block or detect out-of-app ad plugins.
For instance, it takes a little sleep before swinging into action. “These ads do not immediately bombard the user once the offending application is installed, but become visible at least 24 hours after the application is launched,” the researchers said. “For example, obtrusive ads did not present themselves until two weeks after the application ‘Smart Scan’ had been launched on a Lookout test device.”
The BeiTaPlugin also hides its true nature by appending fake file names and suffixes to its components. It names itself “icon-icomoon-gemini.renc” in the system files – purporting to be a legitimate application called Icomoon, which is an application that provides vector icon packs for designer and developer use. One of those icon packs is named Gemini.
“Malware authors commonly employ this technique of renaming executable files to other file types (pdf, jpg, txt) to hide malicious assets in plain sight,” researchers said. “In both cases, the .rec or .renc filetype suffix is intentionally misleading; the file is actually .dex (Dalvik Executable) file type that contains executable code rather than an innocuous .renc file.”
The package is also encrypted, and the AES encryption key is obfuscated through a series of connected methods and finally called for use by a package named “Hades SDK.”
“Increased encryption and obfuscation techniques are applied to hide the plugin’s existence,” explained Lookout researchers. “All strings related to plugin activity are XOR-encrypted and Base64-encoded, courtesy of a third-party library called StringFog. Each class that facilitates the loading of the plugin is encrypted with its own separate key.”
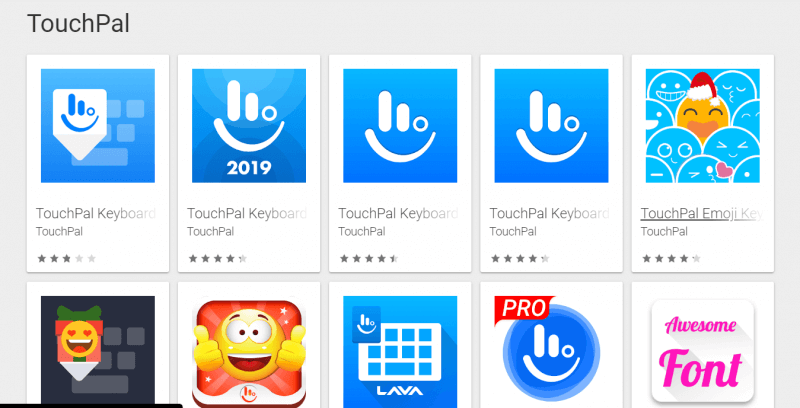
BeiTaPlugin was bundled a popular keyboard app, TouchPal, as well as numerous add-ons to the TouchPal keyboard, and several popular health and fitness apps, according to Lookout. Lookout reported the malicious functionality to Google, and the adware has now been removed from all the affected apps on the Play store – although users with the apps already installed are still likely affected.
Google Play and other app stores are cracking down on the use of out-of-app advertising, so it’s likely that the BeiTaPlugin saga is a sign of things to come, researchers noted.
“This BeiTaPlugin family provides insight into future development of mobile adware,” Lookout said. “As official app stores continue to increase restrictions on out-of-app advertisements, we are likely to see other developers employ similar techniques to avoid detection.”
Article Provided By: threatpost
![]()
If you would like liquidvideotechnologies.com to discuss developing your Home SecuritySystem, Networking, Access Control, Fire, IT consultant or PCI Compliance, please do not hesitate to call us at 864-859-9848 or you can email us at deveren@liquidvideotechnologies.com.

Recent Comments